Set Response Headers
Summary
Set Response Headers specifies a mapping of HTTP Headers to be added globally to all managed routes and Pomerium's Authenticate Service.
How to configure
- Core
- Enterprise
- Kubernetes
- Enterprise via Terraform
| Config file keys | Environment variables | Type | Default |
|---|---|---|---|
set_response_headers | SET_RESPONSE_HEADERS | string | see Default headers |
Examples
JSON
{
"set_response_headers": {
"X-Test": "X-Value"
}
}
YAML
set_response_headers:
X-Test: X-Value
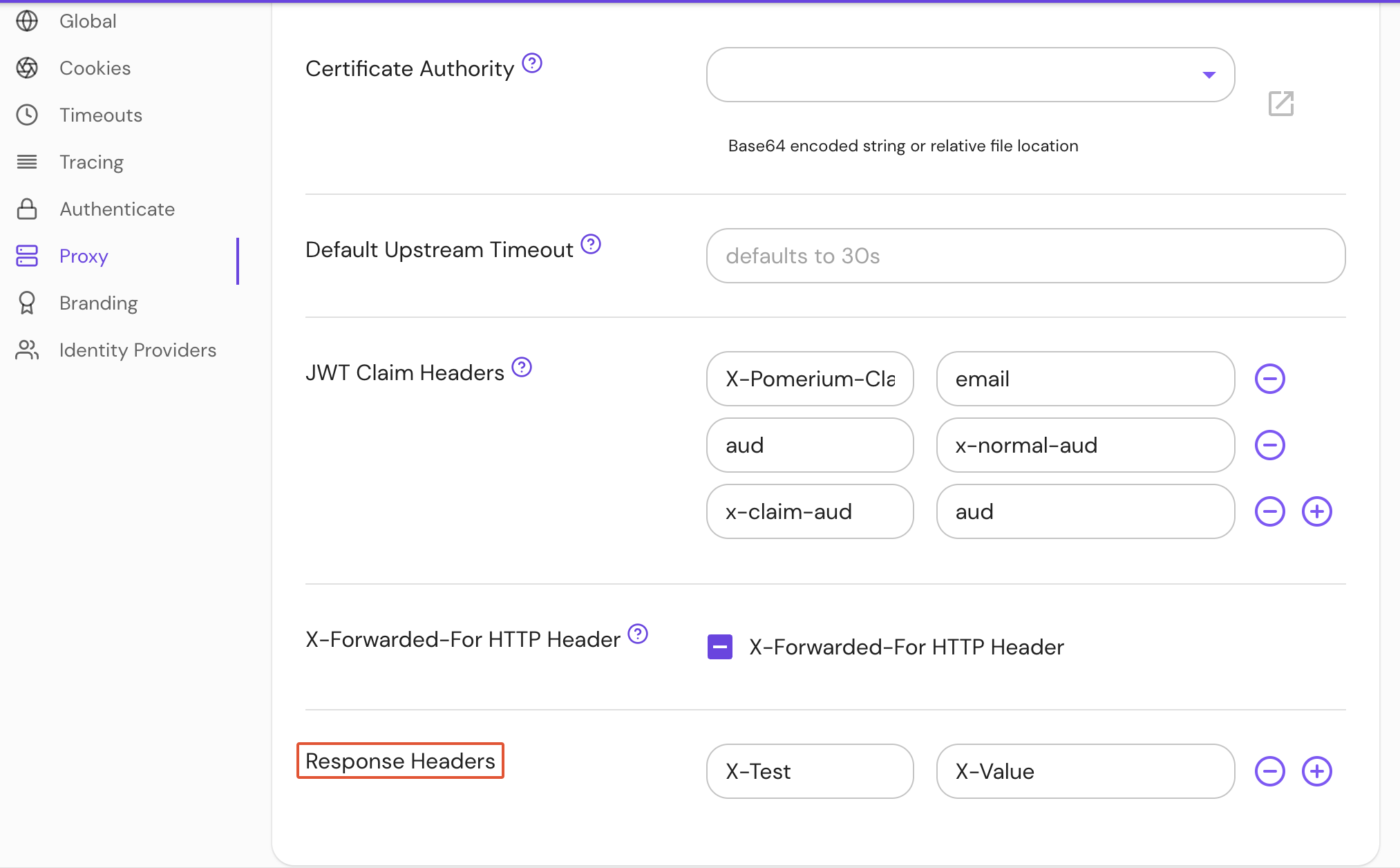
Configure Response Headers under Proxy settings in the Console:
| Annotation name | Type | Default |
|---|---|---|
set_response_headers | string | see Default headers |
Examples
ingress.pomerium.io/set_response_headers: |
X-Test: X-Value
| Annotation name | Type | Default |
|---|---|---|
set_response_headers | Map of String | see Default headers |
Examples
set_response_headers = {"X-Test": "X-Value", "X-Test2": "X-Value2"}
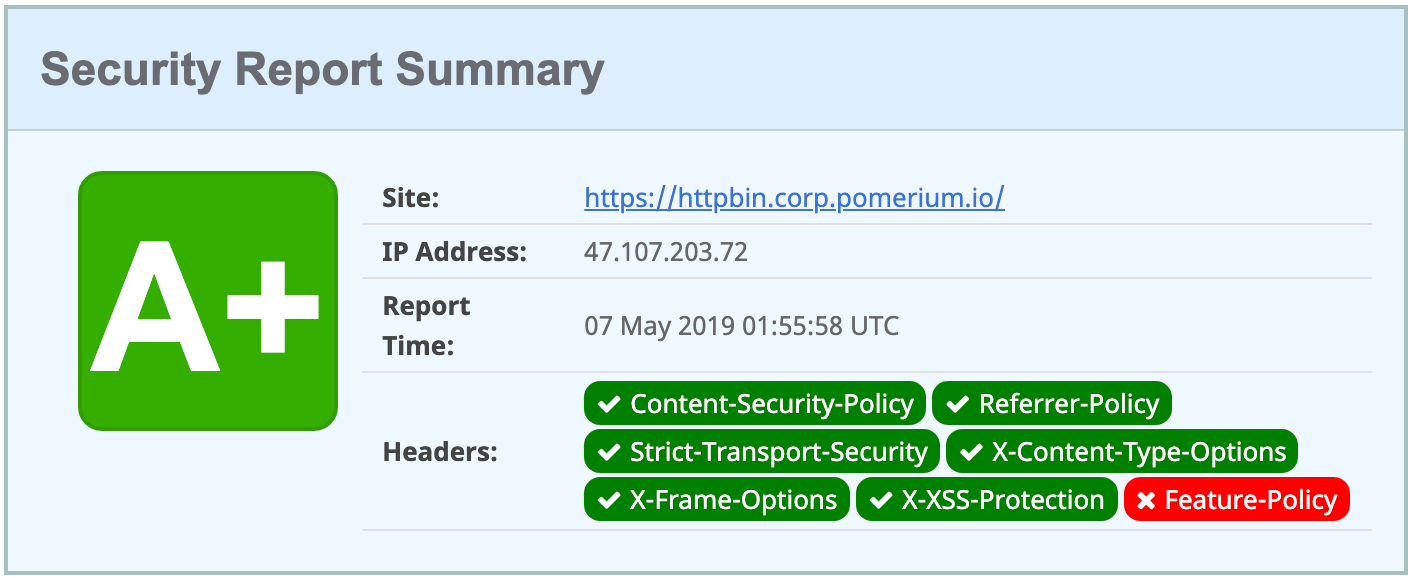
Default headers
X-Content-Type-Options : nosniff,
X-Frame-Options:SAMEORIGIN,
X-XSS-Protection:1; mode=block,
Strict-Transport-Security:max-age=31536000; includeSubDomains; preload,
By default, conservative secure HTTP headers are set:
max-age=31536000instructs the browser to pin the certificate for a domain for a year. This helps prevent man-in-the-middle attacks, but can create issues when developing new environments with temporary certificates. See Troubleshooting - HSTS for more information.includeSubDomainsapplies these rules to subdomains, which is how individual routes are defined.preloadinstructs the browser to preload the certificate from an HSTS preload service if available. This means that the certificate can be loaded from an already-trusted secure connection, and the user never needs to connect to your domain without TLS.
See MDN Web Docs - Strict-Transport-Security for more information.
tip
Several security-related headers are not set by default since doing so might break legacy sites. These include: Cross-Origin Resource Policy, Cross-Origin Opener Policy, and Cross-Origin Embedder Policy. If possible, users are encouraged to add these to set_response_headers or their downstream applications.
Disable response headers
To disable set_response_headers:
set_response_headers:
disable: true